Not known Facts About Risk Management Enterprise
Wiki Article
Our Risk Management Enterprise Ideas
Table of ContentsRisk Management Enterprise - The FactsExcitement About Risk Management EnterpriseNot known Details About Risk Management Enterprise Some Known Incorrect Statements About Risk Management Enterprise Unknown Facts About Risk Management Enterprise5 Simple Techniques For Risk Management EnterpriseGetting My Risk Management Enterprise To Work
Here are some of its crucial attributes that facilities should understand. So, have a look. Real-Time Danger Assessments and Reduction in this software program enable organizations to constantly keep track of and assess threats as they evolve. This function leverages real-time information and automated evaluation to recognize potential risks immediately. As soon as risks are determined, the software facilitates immediate reduction activities.
KRIs fix the trouble of irregular or uncertain threat evaluation. They resolve the difficulty of recurring threat management by offering tools to keep an eye on dangers continually. KRIs improve protection risk oversight, guaranteeing that prospective risks are identified and handled efficiently. The task of risk management need to not be an obstacle. Companies should rely on a top-notch and sophisticated threat administration software.
Top Guidelines Of Risk Management Enterprise
IT risk management is a subset of business threat monitoring (ERM), developed to bring IT take the chance of in line with an organization's threat appetite. IT risk monitoring (ITRM) incorporates the policies, treatments and modern technology needed to decrease risks and vulnerabilities, while maintaining conformity with appropriate governing requirements. On top of that, ITRM looks for to restrict the repercussions of harmful events, such as safety and security violations.While ITRM structures offer useful guidance, it's easy for IT teams to endure from "structure overload." Veronica Rose, ISACA board supervisor and an info systems auditor at Metropol Corp. Ltd., suggests using a combination of structures to achieve the very best results. For instance, the ISACA Risk IT framework lines up well with the COBIT 2019 structure, Rose stated.
Enterprise Risk Management Software Application Development: Perks & Features, Price. With technical developments, risks are continuously on the surge., companies browse through a constantly transforming sea of dangers.
Not known Details About Risk Management Enterprise
In this blog site, we will certainly study the globe of ERM software program, discovering what it is, its advantages, attributes, and so on to ensure that you can construct one for your organization. Business Threat Monitoring (ERM) software application is the application program for preparation, directing, arranging, and managing organization tasks and improving danger management procedures.With ERM, companies can make insightful decisions to enhance the total resilience of the company. Read: ERP Application Development Dedicated ERM systems are critical for organizations that frequently take care of large quantities of delicate information and several stakeholders to accept calculated choices. Some sectors where ERM has actually become a standard system are healthcare, financing, construction, insurance coverage, and info modern technology (IT).
It can be stayed clear of by utilizing the ERM software application system. This system automates guideline conformity administration to keep the organization safe and compliant.
The Facts About Risk Management Enterprise Uncovered
You can additionally connect existing software program systems to the ERM via APIs or by adding information by hand. Organizations can use ERM to examine dangers based upon their potential effect for far better risk management and mitigation.: Adding this feature enables individuals to obtain real-time notifications on their devices concerning any danger that could happen and its influence.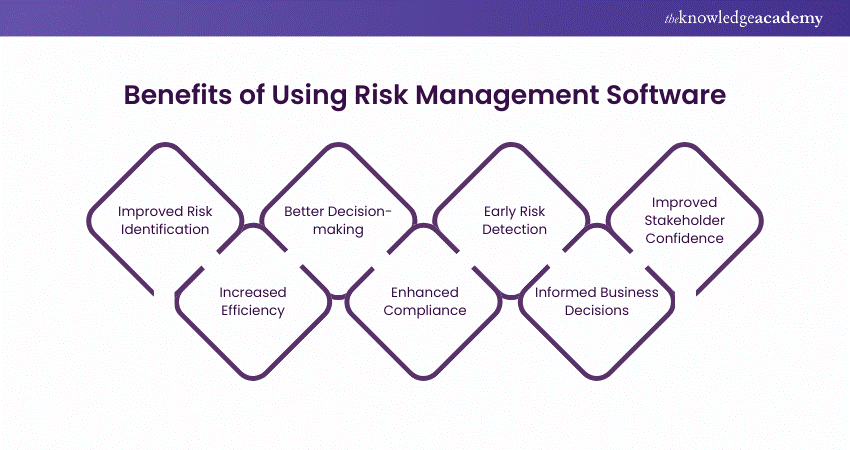
Instead, the software application allows them to establish thresholds for various processes and send push notifications in situation of feasible threats.: By integrating information visualization and reporting in the customized ERM software, businesses can obtain clear understandings regarding risk fads and performance.: hop over to these guys It is obligatory for companies to adhere to sector conformity and governing criteria.

These platforms enable companies to implement best-practice danger management processes that align with industry standards, offering an effective, technology-driven method to identifying, assessing, and mitigating risks. This blog site explores the benefits of computerized risk management tools, the areas of danger management they can automate, and the value they offer a company.
The Single Strategy To Use For Risk Management Enterprise
Groups can set up forms with the pertinent areas and quickly create various kinds for different risk types. These risk evaluation forms can be distributed for conclusion by means of automated process that send out notices to the pertinent team to complete the kinds online. If types are not completed by the deadline, after that chaser emails are automatically sent out by the system.The control tracking and control screening procedure can additionally be automated. Firms can utilize automated process to send out normal control examination notifications and personnel can get in the outcomes via online forms. Controls can likewise be monitored by the software program by establishing guidelines to send informs based upon control data kept in various other systems and spreadsheets that is pulled into the system using API assimilations.
Threat monitoring automation software program can also sustain with danger reporting for all levels of the business. Leaders can check out reports on threat exposure and control efficiency through a variety of reporting outputs consisting of fixed reports, Power BI interactive reports, bowtie analysis, and Monte Carlo simulations. The capability to draw actual time records at the touch of a button removes difficult information control tasks leaving threat groups with more time to examine the data and encourage business on the very best strategy.
Organizations operating in affordable, fast-changing markets can not afford hold-ups or inadequacies in addressing prospective dangers. Traditional threat monitoring utilizing hand-operated spreadsheet-based procedures, you could try this out while acquainted, typically lead to fragmented information, time-consuming coverage, and an enhanced probability of human mistake.
Little Known Facts About Risk Management Enterprise.
This makes sure risk signs up are constantly existing and aligned with business objectives. Conformity is an additional vital chauffeur for automating risk monitoring. Criteria like ISO 31000, CPS 230 and COSO all give guidance around danger administration directory ideal methods and control frameworks, and automated threat management devices are structured to straighten with these requirements helping companies to fulfill most frequently utilized threat monitoring criteria.Seek threat software application systems with a permissions pecking order to quickly set up operations for risk rise. This capability enables you to customize the sight for every individual, so they only see the data appropriate to them. Ensure the ERM software application supplies customer monitoring so you can see that entered what data and when.
Seek out devices that supply task risk monitoring capacities to handle your projects and portfolios and the connected risks. The advantages of adopting threat monitoring automation software extend far beyond efficiency.

The Basic Principles Of Risk Management Enterprise
While the instance for automation is engaging, implementing a threat monitoring system is not without its challenges. To overcome the challenges of danger administration automation, organizations need to invest in data cleansing and administration to make sure a solid foundation for applying an automated platform.Automation in risk administration encourages organizations to change their technique to take the chance of and build a stronger foundation for the future (Risk Management Enterprise). The concern is no more whether to automate risk monitoring, it's exactly how quickly you can begin. To see the Riskonnect at work,
The response typically exists in just how well risks are prepared for and handled. Task administration software application functions as the navigator in the turbulent waters of task implementation, offering devices that identify and evaluate threats and create strategies to reduce them effectively. From real-time information analytics to thorough danger monitoring control panels, these tools supply a 360-degree view of the task landscape, allowing task managers to make informed decisions that keep their tasks on course and within budget.
Report this wiki page